On January 28th, the makers of open source FTP application FileZilla announced that tainted versions of their program are circulating the web. Known collectively as StealZilla, these versions contain malware that steals server log-in credentials and sends them to the attacker.
Identifying StealZilla
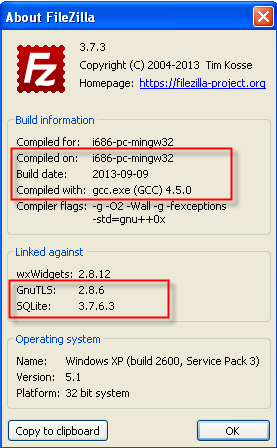
StealZilla is being spread by third-party websites unassociated to FileZilla. If you have recently downloaded what you thought was FileZilla, you should investigate the application’s properties. Pictured below is a comparison of the About Windows from FileZilla (left) and StealZilla (right).
You can also compare SHA1 hashes:
Legitimate InstallerFileZilla_3.7.3_win32-setup.exe:
fd1d51a3070159df19886207133d95b9d53a7106
Malicious Installer v3.5.3:
dee74e8116e461e0482a4fef938b03c99e980e21
Malicious Installer v3.7.3:
f6438315b5a0dc8354b7f1834a1a91aa5c0f09cc
Malicious FileZilla.exe v3.5.3:
749d1c8866b7c0d014b005344e8b6783e53e8d3c
Malicious FileZilla.exe v3.7.3:
9c54e9666c40604e60e69e83337f7ce5de811557
If you require assistance with comparison, please don’t hesitate to contact Emsisoft Support.
How StealZilla Works
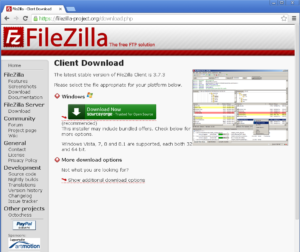
As an open-source application, FileZilla has long been vulnerable to fraudulent replication, however StealZilla is currently the largest and most successful attack to date. At a glance, StealZilla differs very little from FileZilla. To begin, the third-party GUI download sites (right) are almost identical to the official FileZilla one (left).
On top of this, StealZilla is fully functional and the application is only slightly smaller than the 6.8 MB FileZilla.exe. Essentially, StealZilla works because it works – and to the average user nothing appears to be wrong.
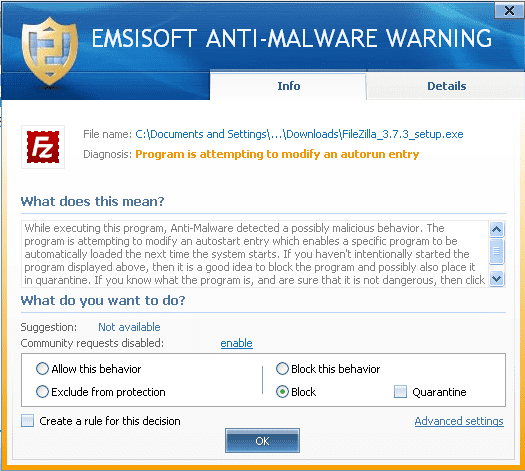
There are a few dead giveaways going on in the background, however. StealZilla actually contains a hardcoded FTP stealer which sends user FTP connection information to the hackers behind the attack. This information is sent only once, but once it is the hackers can then bypass your firewall and perform any number of malicious activities to or with your computer. The is a very subtle method, but Emsisoft Anti-Malware actually recognizes it with its Behavior Blocker.
As yet, the identities of those behind StealZilla are unknown. It has been discovered that the program sends stolen FTP credentials to a server in Germany (IP 144.76.120.24) but the domains linked to this IP are hosted by Naunet.ru, a Russian registrar long associated with hacking. The 3 known domains are: go-upload.ru, aliserv2013.ru, and ngusto-uro.ru but the WHOIS info on these domains is anonymous.
StealZilla Protection
When downloading any open source application it is important to use only official or officially certified websites. For FileZilla, these sites are FileZilla.org and SurgeForce.net. If you use anything else, you are placing yourself at risk. With any application, regular updates are also a key component of comprehensive security. Notably, StealZilla does not allow itself to be updated.
Emsisoft’s Malware Analysis team will continue to follow StealZilla as it evolves, and will keep readers posted if any significant modifications to this threat occur. In the meantime, Have A Malware-Free Day!
Source: http://blog.emsisoft.com/2014/01/30/emsisoft-malware-warning-filezilla-ftp-copycat-stealzilla/